eBay is the World’s Online Marketplace, enabling trade on a local, national and international footing. With a diverse and passionate community of persons and little concerns, eBay offers an online platform where 1000000s of points are traded each twenty-four hours. Mention and explicate the assorted chances offered by ecommerce for concerns.
Autonomic nervous system:
- Tourismand Travel Sector: This sector has updated its system with e- commercialism services. Consumers can do on-line reserves of hotels, motels, air tickets, railroad tickets, etc.
- BankingSector:Most Bankss have changed their on the job manner by doing their services available online through their several web sites.
- HealthCare Sector:This sector is big and uses a major portion of authorities disbursals. So, most wellness attention companies communicate or exchange their services with each other.
- StockSector:In the stock exchange sector, e-commerce services provide demit history installations for clients who can make an overall analysis of the position of the stock countries and do their several minutess.
- Financial Sector: In India, the fiscal sector has adopted e-commerce services and the users make maximal usage of the same.
Advantages of eCommerce:
- Customers can utilize the market place at all times with the usage of e-commerce services.
- Customers are to the full satisfied and receive better service.
- No go-betweens: Customers can straight reach the providers and take all go-betweens.
- Using the e-commerce services, one can understand consumer behaviour, for illustration, websites, merchandises, strategies and manners of payment which are preferred by the client.
- Can salvage clip because they can buy anything through the merchandiser websites.
Disadvantages of eCommerce:
- Peoples who have no cognition about electronic communicating like the Internet, and computing machines find it hard to transact electronically.
- Small business communities do non desire to take any excess load because they have no cognition ofe-commercefunctions.
- Some types of concerns are non fit fore-commerceservices.
- Before implementinge-commerceservices in the concern, it is necessary to finish certain legal formalities like mandate and hallmark.
- High hazard for Internet startup organisation.
- Security jobs
- Customer relation jobs
- Data unity jobs
- Customer satisfaction jobs
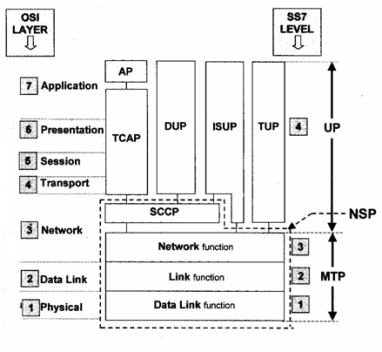
The TCP/IP mention theoretical account is the web theoretical account used in the current Internet architecture. This theoretical account is derived from the OSI theoretical account and they are comparatively same in nature. Explain the different features of Gateways in the TCP/IP mention theoretical account with a orderly diagram
Ands:
Gatewaies provide full protocol transition from one proprietary LAN engineering to another, i.e. Ethernet to token ring or FDDI or any other criterion or protocol instead than encapsulation
It uses higher beds of the OSI theoretical account, possibly through bed 7, the application bed. IBM SNA, DEC cyberspace, Internet TCP/IP and other protocols can be converted from network-to-network
Unlike Bridgess and routers, gateways operate easy because of protocol transition. Consequently, they may make constrictions of congestion during periods of peak use.
Default Gateway
Default gateway consists of manually registering router IP addresses in the host. This method is simple ; and is the most often used. Note nevertheless, that if two or more routers are connected to the same subnet, the web decision maker must find which of these routers the message should be sent to. To work out this job, a message called ICMP redirect is available. Default gateway checks the finish host reference in the standard message. If it determines that the message should be sent via other router, it will direct back a redirect message that includes the IP reference of the selected router, to the beginning host. When the beginning host receives this message, it shops the finish host reference every bit good as the 2nd router reference so that it can direct messages addressed to this host via the 2nd router.
Hypertext Markup Language.
- Hypertextis the method by which you move about on the web — by snaping on particular text calledhyperlinkswhich bring you to the following page. The fact that it ishypermerely means it is non additive — i.e. you can travel to any topographic point on the Internet whenever you want by snaping on links — there is no set order to make things in.
- Markupis whatHTML ticketsmake to the text inside them. They mark it as a certain type of text (italicizedtext, for illustration ) .
- Hypertext markup languageis aLanguage, as it has code-words and sentence structures like any other linguistic communication.
Hanson web sites are built to work for your concern and are built on the construct of intelligent web site. An intelligent web site is more than merely a booklet on the web. It allows you to redact the web site yourself through a Content Management System ( CMS ) . What is the demand for an intelligent web site?
Autonomic nervous system:The demand of intelligent web site is to make the following coevals merchandises, services and models though the research application and survey of information engineering and unreal intelligence.
Following are the stairss companies follow to increase their information.
- Basic Web traffic analysis
- Customer interaction analysis
- Real-timepersonalization
- Geting tofine-grainedsegmentation
- Traveling through the watercourses of chinks
- Enrich content with external informations
- Reaching optimum intelligence.
Basic Web traffic analysis:
In this measure it analyze the Web traffic this provides the information of records of entry & A ; the continuance of viewed, issue point into a web or pages & A ; the nexus they follow.
Customer interaction analysis:
This measure is used to roll up more information about the customer’s interactions with the web site. Registered users through this enrollment procedure, the site is able to acquire information related to both the demographics and penchant. This type of information is used to assist inform personalization engines to function the contents harmonizing to the visitor’s involvements.
Real-timepersonalization:
Personalization is the ultimate realisation of the one-to-one selling dream. Four ways of personalization includes.
- Greetings: This is a more general manner of personalization. The client is greeted by name and welcomed back whenever he or she visits the site.
- Customization: It allows a client to orient the service he or she receives from an e-commerce site
- Recommendation: T was based merely on the penchants that a client would hold explicitly expressed during enrollment. Now, it can be done in existent clip and predicted automatically by the personalization engine utilizing different types of information such as ascertained real-time behaviour, purchase histories and expressed penchants.
- Customization: It allows a client to orient the service he or she receives from an e-commerce site.
Geting to powdered cleavage:
This measure besides uses unreal intelligence to carry on cognition find. That is, it can look for forms in big informations sets and place common elements.
Traveling through the watercourses of chinks:
Click-stream information is the recording of every page petition from every visitant by the web site proprietors. This information is stored into monolithic log files.
Enrich content with external informations:
Once a client performs a figure of purchases, the web site is able to farther heighten the customer’s profile. Demographic information from 3rd party suppliers may be added to the profile to supply a richer position of the client base.
Reaching optimum intelligence:
A company can make optimum intelligence once it is able to unite historical dealing records, observed behaviour via click-stream informations and penchants expressed in on-line studies.